Never has the risk of being hacked and stealing your personal information online been so great. To keep this sensitive data safe, here are some simple tips to use to prevent personal information, if not your identity, from being stolen.
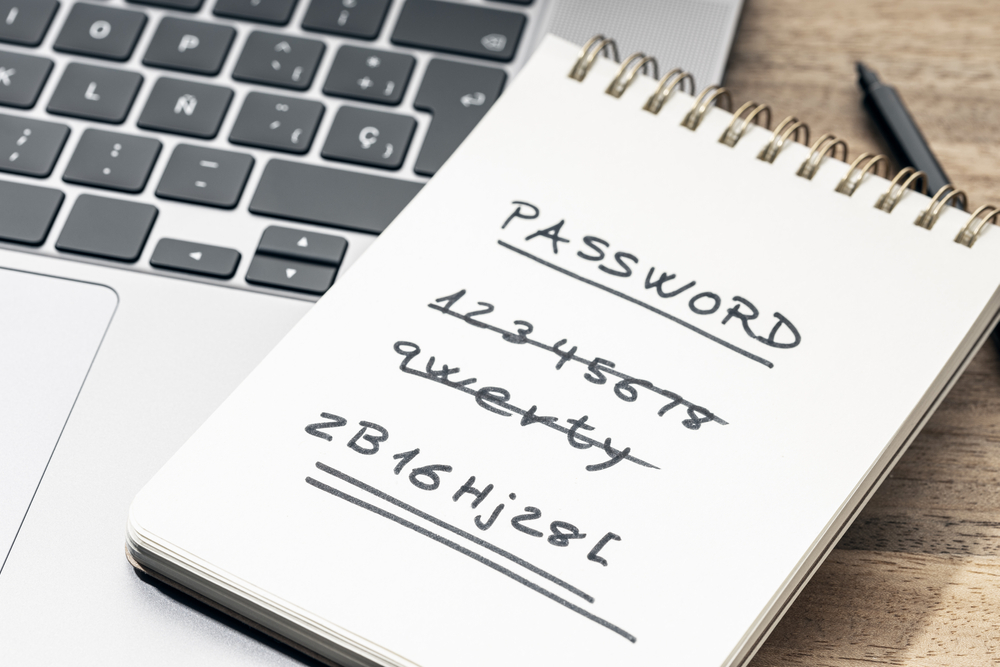
Choose your password correctly
A good password is the first line of defense when it comes to online security. Whatever the service or site, it is imperative to make sure that you choose a password, not just different every time, but as complex as possible, arbitrary, ideally consisting of upper and lower case letters, numbers and special characters, in order to fool malicious algorithms.
Note that there are also many password managers that allow you to refresh them systematically, securely and on all your devices.
Promote multi-factor authentication
If a complex password is required, two-factor authentication promotes even more security of his private data online. This consists of adding at least one extra step to log in to an account. This can take various forms, such as a text message or a personal question. This way, even if your password has been “cracked”, it will still be difficult to access your account.
Create different email accounts
To put all the trump cards on your side, it is also better to create several email addresses to cover the tracks. Indeed, the address is often the identifier for a site or an online service and it is therefore recommended to use different email addresses depending on the use (one for the different social networks, another for the commercial sites, etc.). Also note that it is quite easy to create aliases from your main account.

Avoid sharing your location
Mobile devices continuously determine and register your location and it is even easy to share it with friends, for example on a date. If your smartphone’s GPS is particularly useful for getting your bearings and getting around, this is much less the case in terms of safety. It is therefore preferable to disable this location sharing on all its devices and allow access to the GPS only to the applications that really need it.
Spring clean your phone
On a smartphone or tablet, you should regularly search your applications and do not hesitate to delete all those applications that are never asked. The same goes for the cache, this temporary information that is kept on the terminal, but which you can delete without risk.
To go further, find everything you need to know about the dangers of the Internet in this small online glossary.
(ETX Daily Up)